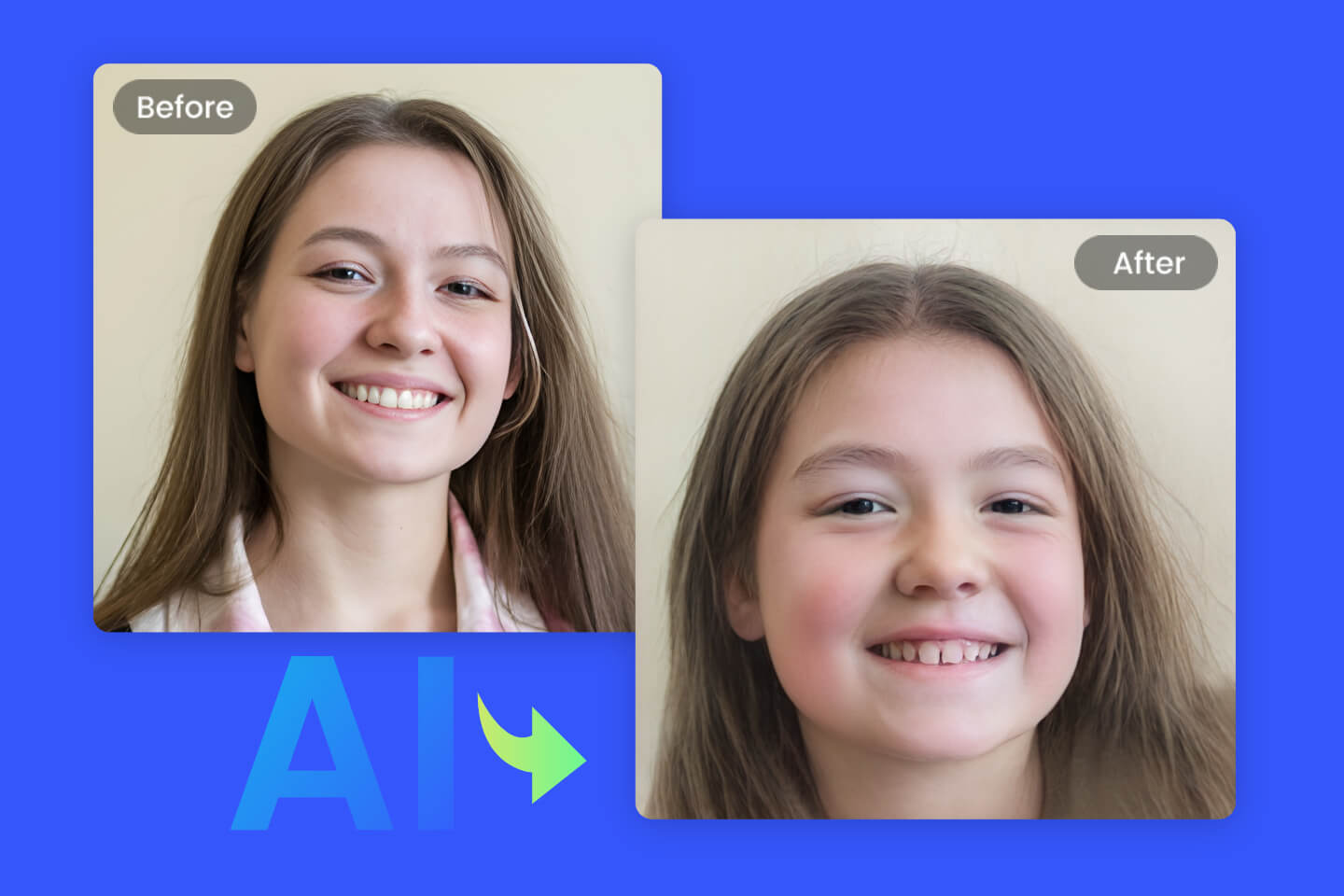
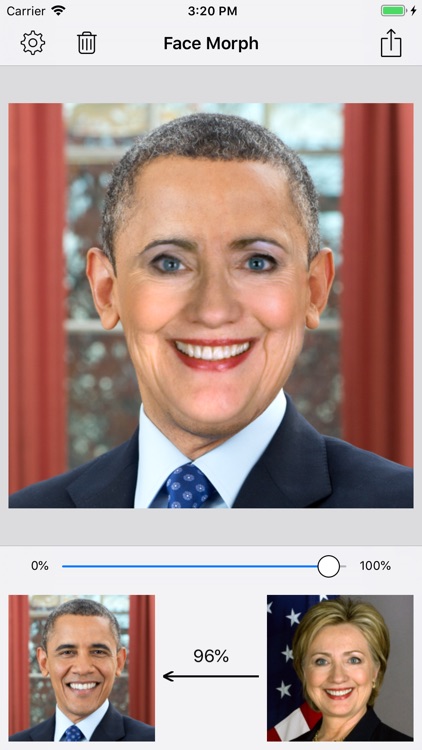
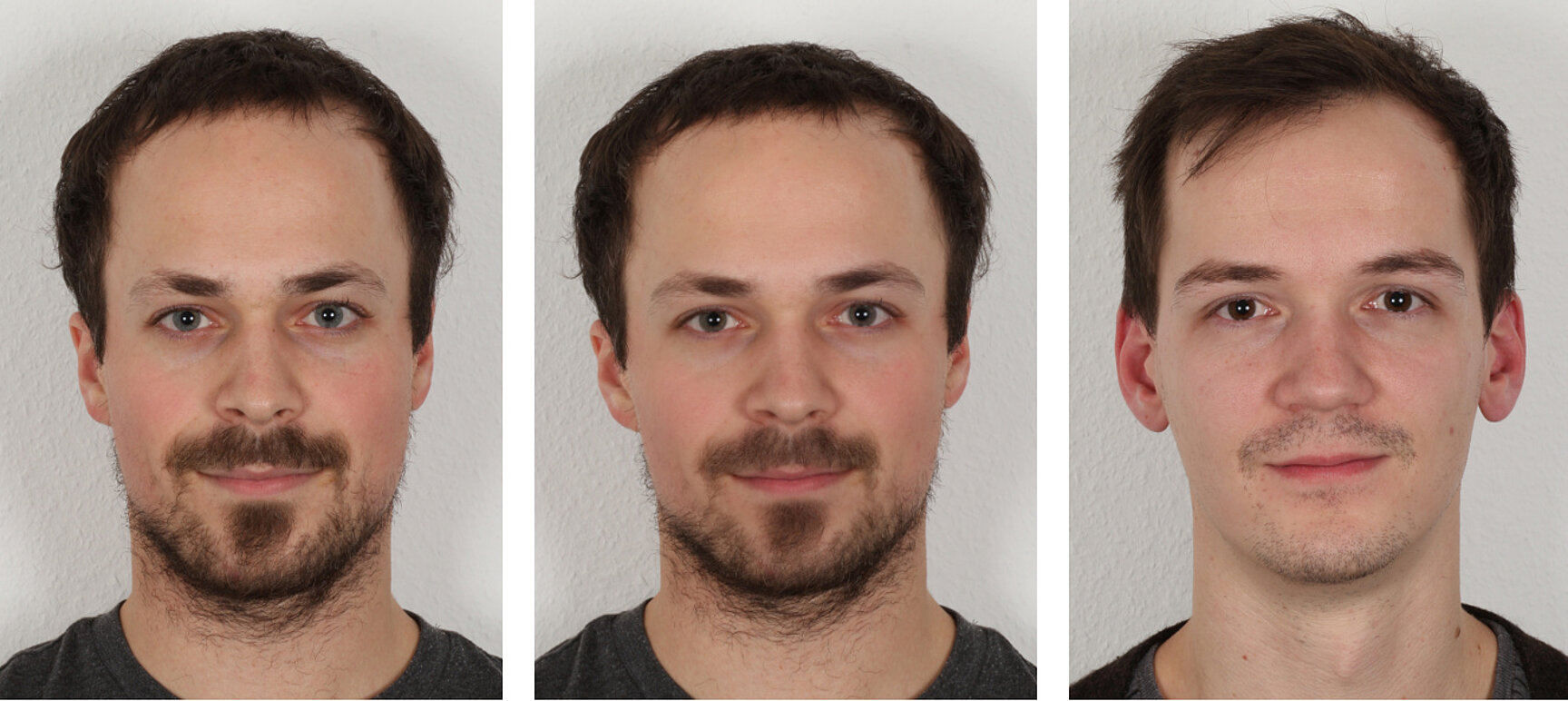
Face morphing attacks: Investigating detection with humans and computers | Cognitive Research: Principles and Implications | Full Text

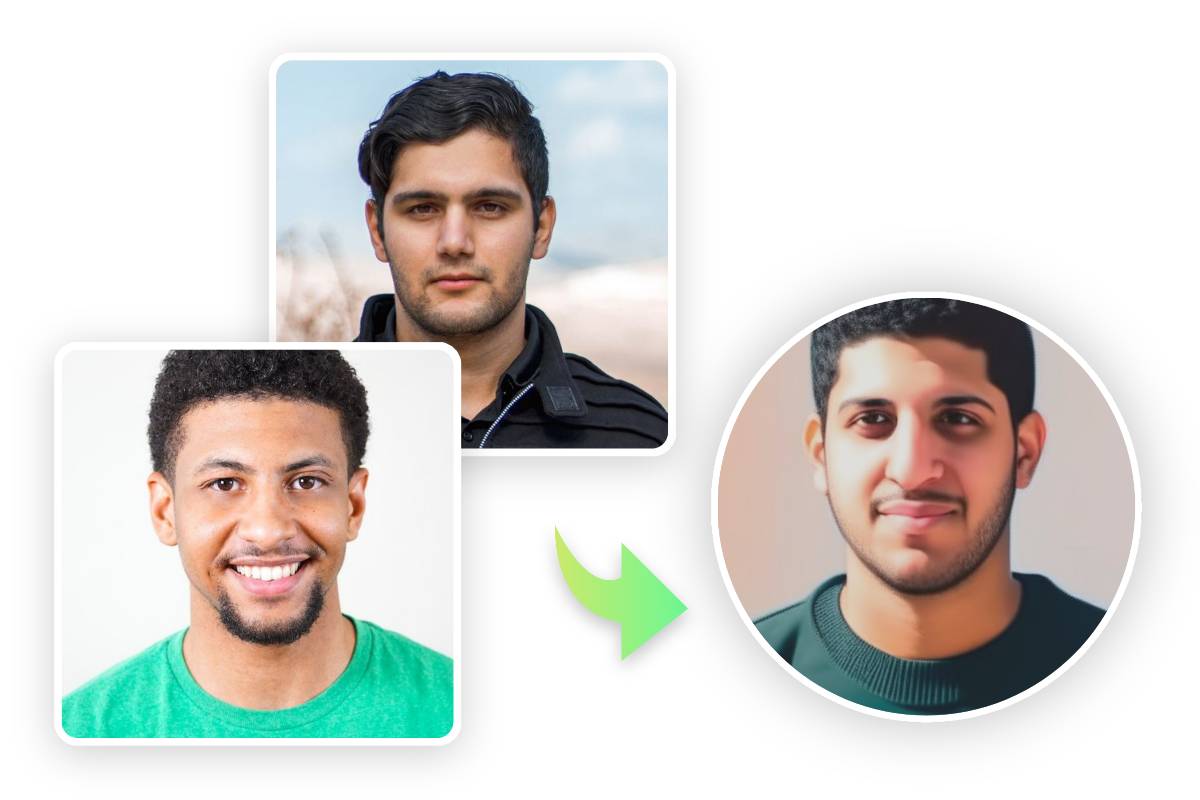
Applied Sciences | Free Full-Text | A Comprehensive Review of Face Morph Generation and Detection of Fraudulent Identities

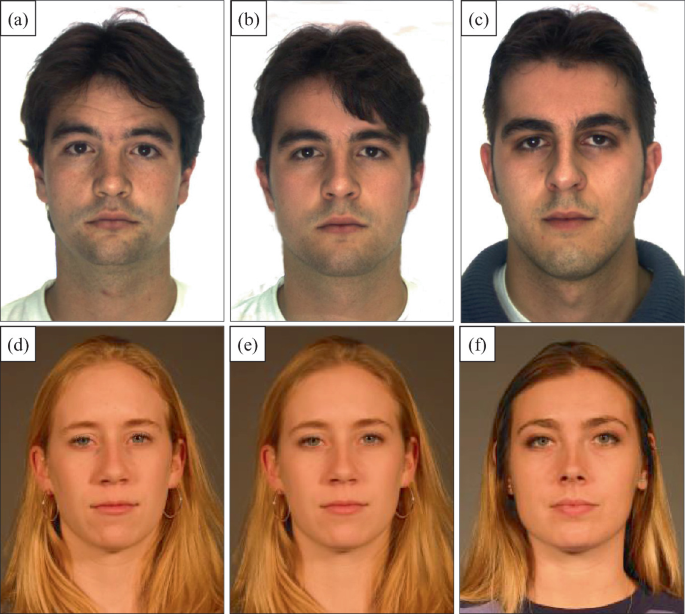
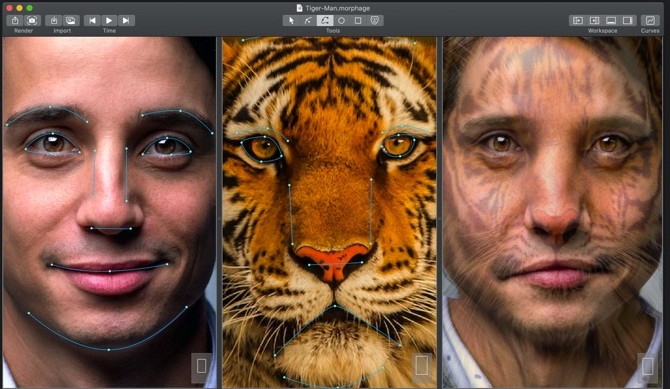
Medium Face morphing Comparison: (a) MorphThing result, (b) Proposed... | Download Scientific Diagram